Code obfuscation, which is an important part of software development, helps to protect sensitive code, credentials, and valuable information from getting into the wrong hands. To ensure that your code is secured, you need to be aware of the different methods and strategies surrounding code obfuscation. This article will cover the top things to keep in mind about code obfuscation.
Table of Contents
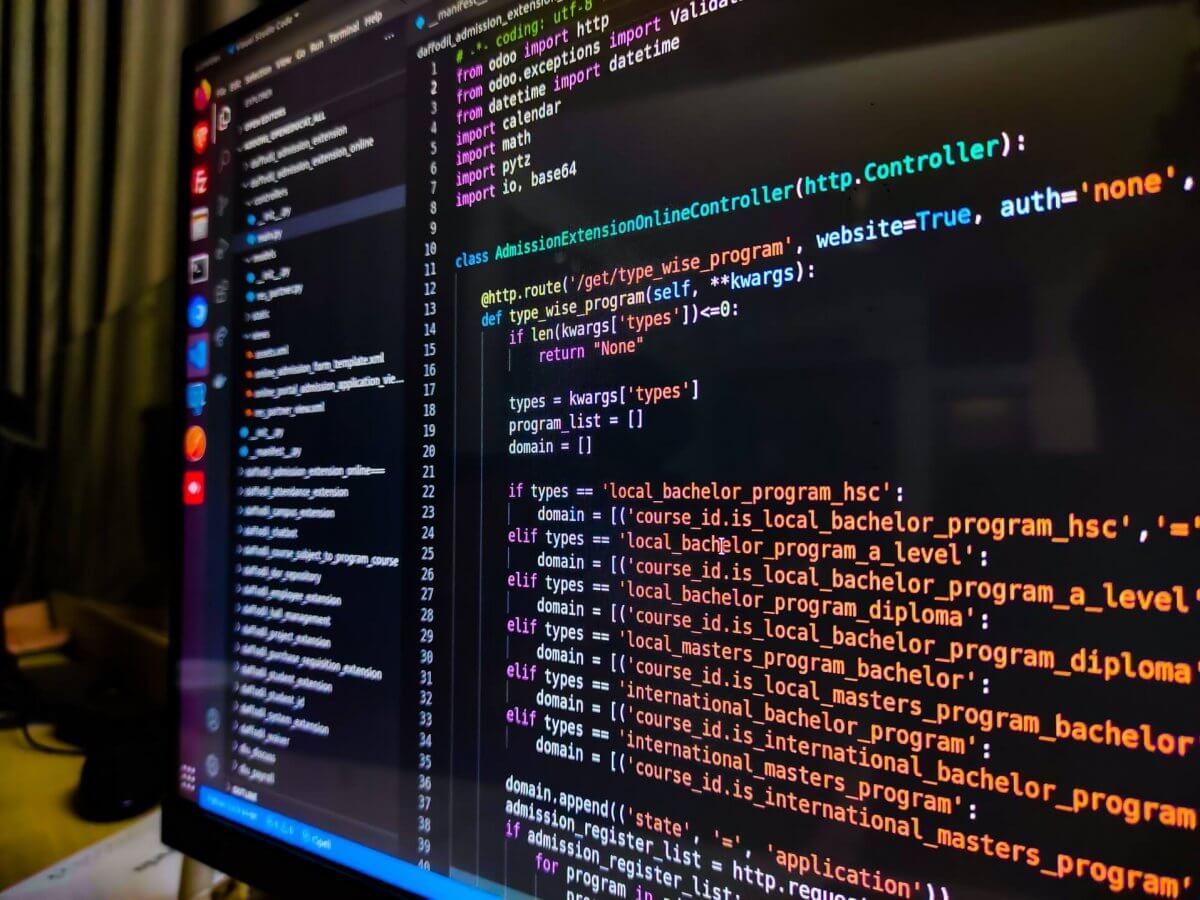
What Is Code Obfuscation?
Code obfuscation is the process of making code difficult to read and understand for attackers or competitors who are looking to steal software or code. It involves altering code to make the underlying source code difficult to read or disassemble, which can make it harder to attack or potentially reverse engineer. This is done to protect the code from unwanted individuals and from being used maliciously. Code obfuscation can also be used to hide information from competitors and provide protection against reverse engineering.
Benefits of Code Obfuscation
There are many benefits to code obfuscation. It can help protect software from crackers, help to reduce the size of binary code and make reverse engineering more difficult. Additionally, code obfuscation can help to reduce the download size of your software, speed up code execution, and make the development process smoother. It can also help protect your intellectual property rights and reduce the risk of third-party data abuse.
Drawbacks of Code Obfuscation
The main drawback of code obfuscation is that it can be time-consuming and costly to implement. Additionally, it can be difficult to maintain obfuscated code, as it is often difficult to debug or modify due to the convoluted code. It is also important to note that code obfuscation does not guarantee complete security, as attackers can still potentially breakthrough code obfuscation with the right skills and the right tools.
Examples of Code Obfuscation
There are a few different examples of code obfuscation. The most common types are renaming variables and methods, stripping comments and metadata, and writing algorithmically complex code. Additionally, developers can encrypt strings, add unreachable code, and use multiple layers of encryption for added protection.
How to Implement Code Obfuscation?
The best way to implement code obfuscation is to use a combination of techniques. At a minimum, this should include renaming variables, stripping comments, and encrypting strings. Additionally, developers should also consider using logic-based techniques (like adding unreachable code or writing more complex algorithms) and implementing multiple layers of encryption.
Different Types of Code Obfuscation
There are several different types of code obfuscation, including renaming variables and methods, stripping comments and metadata, writing complex algorithms, using multiple layers of encryption, and adding unreachable code. Each of these techniques can be used in combination with one another to effectively protect your code.
What Is Not Code Obfuscation?
Although code obfuscation can be an effective technique for protecting code from malicious actors, it is important to note that it is not the same as encryption or white-box cryptography. While code obfuscation does make it more difficult for attackers to gain access to the underlying source code, it does not offer the same level of security as encryption or white-box cryptography.
Popular Obfuscation Tools
There are several popular tools available to developers that can be used to easily and quickly implement code obfuscation. Additionally, many popular development technologies (have code obfuscation libraries that can be easily integrated into the development process.
Best Practices for Code Obfuscation
For code obfuscation to be effective, it is important to adhere to best practices. This includes using multiple layers of obfuscation to make it more difficult for attackers to gain access to the underlying source code, making sure to regularly test and monitor the code, and keeping code obfuscation up to date with the latest obfuscation techniques. Additionally, developers should avoid over-obfuscating code, as this can make it difficult to maintain and debug.
How To Ensure The Best Code Obfuscation?
Have you been worrying about how to ensure the best code obfuscation? If so, you have come to the right place! Obfuscating your code is a crucial part of the development process and it is important to do it effectively. In this article, we will discuss the different methods and techniques of code obfuscation and provide some tips on how to make sure you are doing it correctly. So, let’s get started!
The Benefits of Code Obfuscation
Code obfuscation comes with many benefits. By obscuring the code, it is much harder for perpetrators to gain access to the code and use it for their malicious purposes. This improves the security of the software and reduces the risk of a data breach. Additionally, code obfuscation can reduce the overall size of the software, making it more efficient and easier to distribute. Finally, it discourages software tampering and can make reverse engineering more difficult.
Techniques of Code Obfuscation
There are several techniques for code obfuscation. These include renaming variables, embedding code in loops, using random numbers or strings, using multiple coding languages, and using encryption. Renaming variables makes it difficult to decipher the code by changing meaningful names to too difficult or Generic-looking names. Embedding code in loops makes it harder to identify individual pieces of code as they are hidden among many other instructions. Additionally, using multiple coding languages and using random numbers or strings can help hide the code and make it harder to reverse engineer. Finally, using encryption makes it difficult to break through the code as it requires the proper keys and encryption techniques.

Tips for Ensuring Best Code Obfuscation
There are a few tips to ensure the best code obfuscation. First, it is important to use multiple techniques to make sure your code is as secure as possible. This could include renaming variables, embedding code in loops, using random numbers or strings, using multiple coding languages and using encryption. Additionally, it is important to keep the code as simple as possible to make sure it is secure. Complex code can be difficult to understand and debug and can be easier for malicious users to access. Finally, it is also beneficial to keep a backup of your code, which can help protect your intellectual property and make it more difficult to tamper with.
Conclusion
Obfuscation is an effective technique for protecting code from malicious actors. It involves altering code to make it difficult to read or disassemble and to also protect intellectual property rights. This article covered the top few things to keep in mind about code obfuscation, including the benefits and drawbacks, how to implement code obfuscation, the different types of code obfuscation, and best practices for code obfuscation.